Our Services
Tailored IT solutions to secure and streamline your operations.


IT Security
Why IT Security Services Matter
Organizations today rely on technology to store critical data, communicate, and operate efficiently—making security a top priority. A comprehensive IT security approach helps protect systems from threats, minimize downtime, and ensure business continuity.
Key components of a strong security posture include reliable data backups, endpoint protection, and email security. Backup systems ensure that data can be quickly restored in the event of ransomware, system failure, or accidental loss. Endpoint protection safeguards devices such as computers and servers from unauthorized access and malicious activity. Email filtration reduces the risk of phishing attacks, spam, and harmful attachments that can compromise an entire network.
By implementing layered security measures, organizations can significantly reduce risk, maintain operational stability, and protect sensitive information.
At Central Valley Solutions LLC, we provide practical, effective security strategies designed to keep systems secure, resilient, and prepared for evolving threats.
Policy Development
Why IT Policies Matter
Well-defined IT policies provide the foundation for secure, consistent, and accountable technology operations. They establish clear expectations for how systems are used, managed, and protected, helping organizations reduce risk and operate more effectively.
Strong policy frameworks include cybersecurity awareness training to reduce human risk, governance structures that define roles and responsibilities, and disaster recovery planning to ensure continuity in the event of an incident. In addition, properly documented policies support compliance with regulatory requirements and help organizations confidently navigate audits and reviews.
By aligning technology practices with documented standards, organizations can improve security, strengthen accountability, and ensure long-term operational resilience.
At Central Valley Solutions LLC, we develop practical, tailored IT policies that support security, compliance, and sustainable operations.
Operations Review
Why Use a Third-Party for IT Operations Review
Technology plays a critical role in supporting daily operations, protecting sensitive data, and enabling long-term growth. An independent IT operations review provides an objective assessment of systems, security, and processes, helping organizations identify risks, improve efficiency, and align with industry standards.
A third-party perspective brings specialized expertise and unbiased insight, uncovering gaps that may be overlooked internally. This approach not only strengthens security and performance but also supports internal teams with clear, actionable recommendations.
At Central Valley Solutions LLC, we help organizations enhance operations, reduce risk, and maintain reliable, secure technology environments.


Additional Services

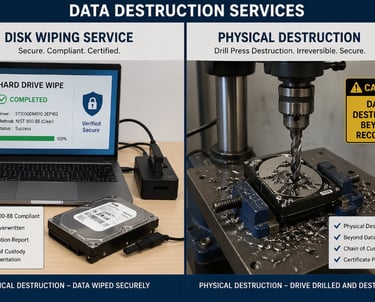
Data Disposal
California Civil Code §1798.81:
Requires businesses and agencies to:
“Take all reasonable steps to destroy…customer records…to make them unreadable or undecipherable”
We perform Perform data wipe (NIST 800-88 compliant) OR Remove drives for separate destruction
Pricing
Pricing for equipment pickup varies based on volume, however, hard drive destruction is typically $20 per drive. This rate includes secure data wiping, physical destruction, comprehensive asset tracking and documentation, and compliant e-waste handling and disposal.
e-Waste Pickup
We will coordinate on-site collection of displays, TVs, workstations, and printers, ensuring all assets are properly inventoried and tracked. Our team will document the e-waste drop-off process and maintain a clear chain of custody. Upon completion, we will provide all required documentation, including disposal records and any applicable certificates of recycling or destruction.
Please note: Additional charges may apply for the disposal of battery backup units (UPS) due to specialized handling requirements.
Contact Us


Reach out to central valley solutions for trusted IT consulting support.

Contact
connect@centralvalleysol.com
© 2025. All rights reserved.
